Remote Desktop Protocol (RDP) has become an important tool for managing company networks in an era of hybrid workspaces. However, an unsecured RDP endpoint makes a vector that offers cybercriminals significant benefits when they attempt to attack your systems. What malicious activities might threat actors perform via RDP, and how do you prevent them from doing so?
What is an RDP endpoint?
It is a Windows device that is running Remote Desktop Protocol (RDP) software so that it can be accessed over a network, such as the internet. RDP enables an organisation’s Windows devices to be accessed remotely as if their keyboards and displays were on your desk. It can help with managing or troubleshooting employee devices, serving up centralised resources such as desktops that can run heavy workloads, applications, databases and many others.
The number of incidents using an RDP endpoint in the past few years has been on the rise
More frequently attackers took advantage of connecting to Windows Servers from the internet using RDP while logging on as the computer’s administrator. This might have been done by exploiting vulnerabilities (such as BlueKeep CVE-2019-0708), phishing, credential stuffing, password spraying, brute force or poorly configured access to internal systems. Once attackers are in, they typically try to determine what the server is used for, by whom and when it is being used. Malicious actions are to follow.
The most common malicious activities performed via RDP:
- Installing ransomware
- Installing cryptomining programs to generate cryptocurrency (such as Monero)
- Installing additional remote-control software to maintain access to compromised servers in case RDP activities are discovered
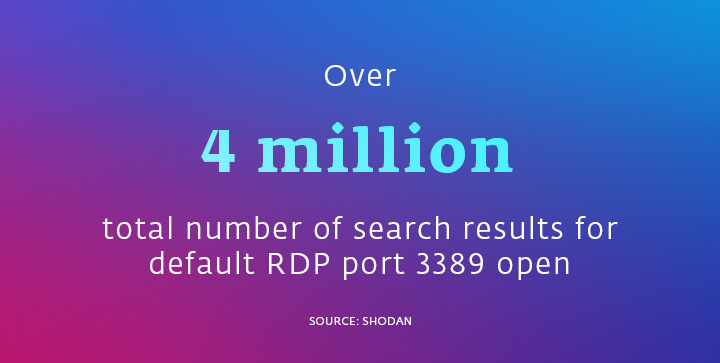
The main vulnerabilities that lead to an attack via RDP are weak login credentials. Due to these, RDP is at risk of brute-force and credential stuffing attacks. Unrestricted port access represents another issue – most RDP connections use default port 3389, which opens a route for attackers.
Using unsupported OS or not updating to the latest version opens door to exploits and vulnerabilities. For example, BlueKeep is a security vulnerability that largely affected Windows 2000, Windows XP, Windows Vista, Windows 7, Windows Server 2003, Windows Server 2003 R2, Windows Server 2008 and Windows Server 2008 R2 in May 2019 and continues to impact IT infrastructure even now. The BlueKeep vulnerability allows attackers to run arbitrary program code on the victims’ computers. Even though individual attackers can also present a widespread threat using automated tools for attacks, BlueKeep vulnerability is “wormable.” That means an attack can spread itself automatically across networks without any intervention by users.
Apart from that, finding systems accessible from the outside and then abusing them for malicious purposes is straightforward for the criminally inclined. Why? Vulnerable RDP systems are quite easy to find. For example, systems running RDP can be identified by specialised search engines like Shodan, which constantly scour the internet for connected devices and collect information about them. As of August 2021, Shodan indicated that there were over 4 million systems on the internet with RDP port 3389 open.
It is also easy for attackers to obtain a foothold on RDP systems if they have poor configuration. Tools and techniques for escalating privilege and obtaining admin rights on compromised RDP systems are widely known and available.
Using the RDP safely
If you want to use Remote Desktop Protocol safely, limit RDP access to specific roles and systems that are configured securely, patched promptly, monitored constantly, firewalled appropriately and backed up regularly. Make sure everyone is complying with the company rules of using RDP and make an inventory of your internet-facing assets – it is not unusual that an organisation is attacked via an internet-connected asset that the security staff were not aware of until after that attack. That’s why you need processes in place to ensure that this does not happen to your business.
Once you have the inventory of internet-facing assets done, document which ones have remote access enabled, and then decide if that access is necessary. If it is, follow the rules below.