When employees leave a company, predefined IT and HR processes for so-called offboarding are usually taken for granted. The process often involves, for example, returning access cards or hardware – fairly mundane tasks. However, that is not the case with IT security, which tends to be neglected. Possible consequences? Threats to security and undesirable data leakage.
The reasons for quitting a job may vary; however, not every parting is mutually agreed upon. Before workplaces were digitalized, ex-colleagues might perform their jobs poorly to take revenge on the employer. But nowadays, angry soon-to-be-ex-employees can harm the company’s digital security by secretly copying confidential data, stealing business contacts or even manipulating or deleting vital files from the company´s network. According to various surveys, this happens particularly frequently in the technology, financial, management and consulting sectors. What might be seen as just a bit of rebellion in the offline world can turn into a criminal offense in the digital world.
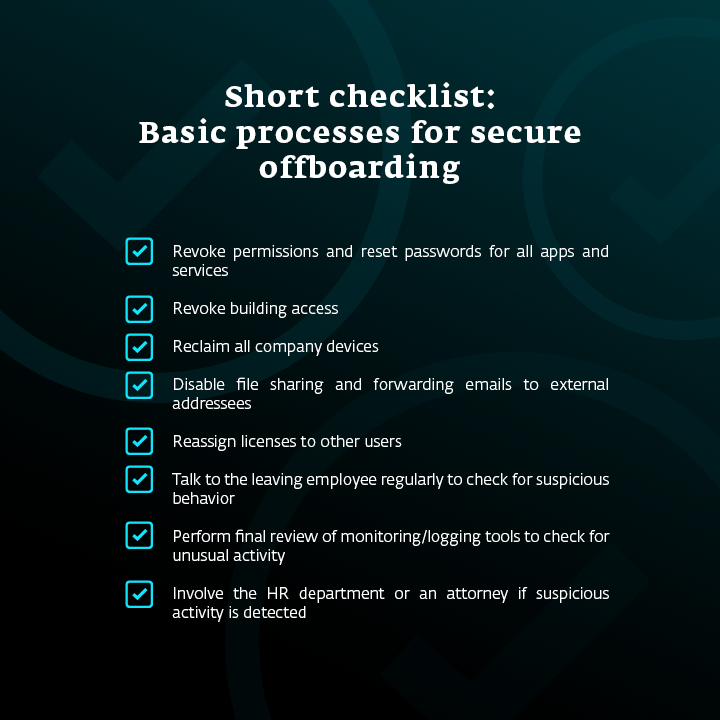
Therefore, when it comes to offboarding employees, the IT security department should play a central role. The measures should go far beyond collecting access cards, laptops and smartphones and deactivating the employee’s email. All access to messaging platforms, online tools, cloud services and networks must be denied.
Avoid incidents and damage
Whether employees steal data to impress a new employer, or simply take or delete it out of resentment, the potential impact on the business can be severe. The resulting data leaks can have the following consequences, among others:
• Investigation, remediation and cleanup costs
• Legal costs from lawsuits, including class-action lawsuits
• Regulatory fines
• Brand and reputational damage
• Loss of competitive advantage

From co-worker to saboteur
The offboarding process can become particularly tricky if the departing employee made the decision to leave the company in advance, and simply hadn’t informed management of his or her intentions. In this case, the employee may represent a potential danger over a longer period of time. Experts often classify such insiders as a security risk due to their negligent behavior or criminal intentions.
The European Union Agency for Cybersecurity (ENISA) has also addressed the problem of insiders and included it in the list of top 15 threats. The 2021 Threat Landscape Report shows that insiders are directly responsible for data losses of all kinds. This group of employees is more likely to get involved in social engineering attacks, which, together with malicious e-mails and manipulated links, belong to the most dangerous attack vectors. It doesn't matter whether the departing employee/insider simply acted negligently or deliberately opened the gates for hackers; the danger posed by internal perpetrators needs to be addressed.
Tips for secure offboarding
1. Communicate policies in a clear and understandable way
Your employees may think that the data they produce at work belongs to them. Clear and structured policies help them better understand the limits of their involvement in intellectual property. In addition to the corresponding guidelines, include clearly formulated sanctions in the event of noncompliance. It is advisable to back up these specifications with concrete examples, using customer lists or technical drawings as case studies. While these documents might have been created by the employees, they in fact belong to the company.
2. Rely on continuous monitoring
Use control technologies that continually monitor and report suspicious activity, while respecting local data protection laws.
3. Define concrete guidelines and processes
What’s already considered standard when it comes to onboarding new employees is often neglected when employees leave. If you define workflows and processes in advance, you create optimal conditions for seamless and effective offboarding.
4. Perform regular backups
Don’t let offboarded employees steal your data and then delete it. Use effective data backup and recovery solutions to make sure you always have a copy and can ensure business continuity. “Combine cloud and local backup solutions and meet the 3-2-1 rule: have three copies in two different internal locations and at least one outside the company,” says Greg Bak, the product development manager at Xopero Software.
Backups can be a useful preventive measure.
5. Try data loss prevention (DLP) software
Prevent unauthorized parties from accessing and sharing internal data by implementing reliable data loss prevention software. It also helps you manage your data flow and stay informed on how it’s being handled. The DLP software offered, for example, by Safetica also helps you detect insider threats while complying with data privacy regulations.
6. Store data in the cloud
Another preventive measure? Don’t only rely on hard drives, and ask employees to always store data in the cloud – preferably even the work-in-progress files – so that it is accessible to more users. The drive in an employee’s computer or other device should never be the only place where the data is kept.
In the digital era, businesses can no longer afford to have their valuable intellectual property stolen by anyone, especially by departing employees, who might have handled sensitive data while working at the company. Whether caused consciously or unconsciously, data leaks can harm the company image and cause financial damage. Therefore, careful offboarding should become an integral part of your company’s IT security.