Your IT infrastructure should be like an unconquerable fortress. The more layers of protection, the less chance the consequences of a cyberattack will be devastating. But when it comes to crunch time, people tend to make mistakes – especially when they’re working remotely. If you want to avoid data breaches, use two-factor authentication and encryption on all devices.
This is an audio version of the article:
Did you like it? Let us know what you think about this initiative by completing a 2-min survey.
Even before the huge jump in numbers of people moving to remote work in response to the COVID-19 pandemic, more than 7% of remote users or devices had been successfully phished. According to a 2019 IBM Security – Cost of Data Breach Report, 49% of inadvertent breaches studied happened due to human error.
This often occurs on devices that were lost in the work area or vehicle. To prevent cybersecurity issues linked to remote work, and to ensure the continuity of your business, you should extend the protection of your devices and sensitive data as much as possible. The right encryption solution and the implementation of two-factor authentication can help you with that.
Encryption: A Shield Against Computer Viruses and Fines
Encryption is the process of encoding information so that it can not be accessed by unauthorised persons. If your company’s encrypted data is leaked, anyone who steals the data will not be able to read it without the proper decryption key. This process is designed to protect money and valuable information. And in the business environment, encryption should also be used to protect intellectual property, know-how, or personal data you process within your company.
All companies have customer lists, proprietary information, sales-related data, or staff and HR information that shouldn’t fall into the wrong hands. We can imagine a scenario in which an employee loses their smartphone, one with weak password security, which may ultimately lead to unintentional exposure of some sensitive data. Or another, in which an employee may bring a personal laptop to work, unfortunately one that contains malware that allows its operator to make changes to the administrative rights, security settings or other sensitive inputs.
Now, if your data is not encrypted, anyone can read it. And it might be released, publicised, or used for other malicious purposes.
If you want to avoid such a situation, think of implementing an encryption solution that makes it virtually impossible for hackers to read stolen data. An encryption solution provides you with the ability to immediately terminate remote users and render data on any device inaccessible, thus effectively mitigating the risk.
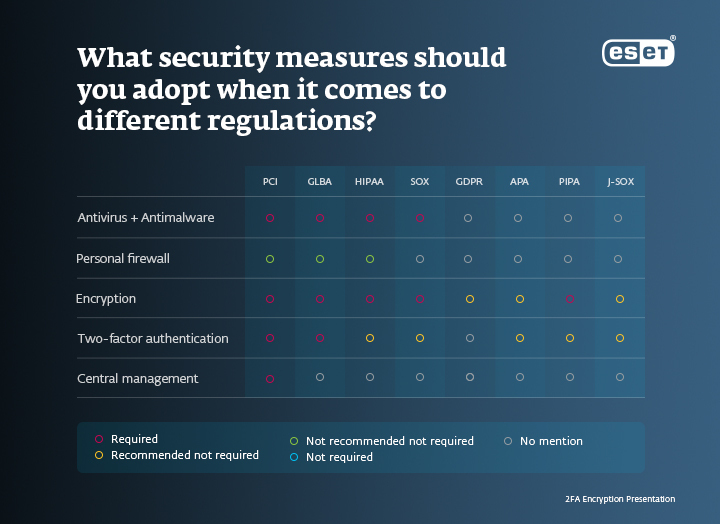
Also, many regulations and laws, including GDPR, PCI-DSS, HIPAA, SOX, and GLBA, require encryption. If personal data is properly encrypted, data breach incidents are much less likely to be regarded as compliance failures.
What Does Two-Factor Authentication Add to Your Business?
Two-factor authentication (2FA) is a method used to verify a user's identity when he or she is trying to access an application. It doesn’t end when the user types in a username and password. On the contrary, 2FA requires you to provide a second piece of information to confirm your identity, such as a verification code, answers to personal security questions, or biometrics like facial recognition or a fingerprint scan.
Good password hygiene is crucial but difficult to maintain for many businesses. According to Dashlane, in 2018, the average American had around 200 digital accounts that required a password to access. Which also means 200 passwords to remember (even though two-thirds of people use the same password for all logins). Some experts predict that password use will explode further, before passwords eventually fade, replaced by new technology.
But until this happens, here are a few reasons, published in The Business Journal, to illustrate why every business should require 2FA (not only for cloud platforms). First, 90% of passwords can be cracked in less than six hours. Moreover, cybercriminals are able to test billions of passwords every second. Eventually, by breaching passwords, hackers can bring your company down – just like they did in the case of Xander Koppelmans, whose story we recently shared.
Companies that use cloud-based software or have employees sign in through a virtual desktop should require 2FA for everyone, because it lowers the probability of breached passwords and entry of uninvited guests into their network in case a device is lost or stolen. It also protects you against phishing emails. If someone sends you a fraudulent email that tries to trick you into logging in with your username and a password to a fake site, 2FA can still protect you, because only the legitimate site will send you a working 2FA code. Encryption and 2FA will help you build more secure IT infrastructure, both in-house and with remote workers.