Without buy-in from executives, a lot of IT security experts have their hands somewhat tied. Fortunately, CEOs in general have become more concerned about cybersecurity over the past year. Yet some still do not entirely grasp why IT security experts need more financial support. So what can you do about it?
Several points of view were brought forward by Infosecurity Magazine, which recently hosted a live webinar on How to Win Budget & Buy-in from the C-Suite to Mitigate Increased Threats, including a panel discussion about the current situation regarding investments in cybersecurity across companies. How has the cybersecurity landscape evolved since the start of the COVID-19 pandemic, and has the rise of cyber threats fuelled cybersecurity funding in companies all over the world?
Half of businesses fell victim to a cyber attack or security breach in 2020.
207 days was the average time needed to identify a breach in 2020.
Source: IBM Cost of Data Breach Study 2020
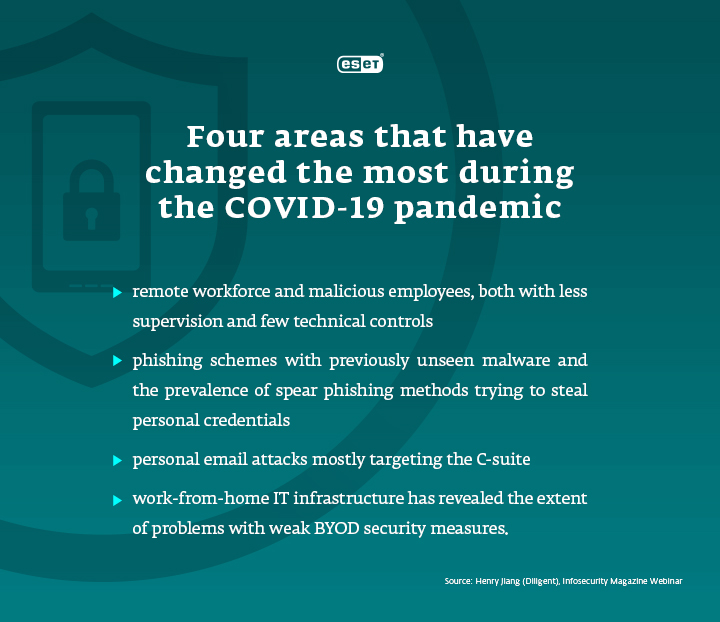
Many companies weren’t prepared to secure personal devices when workers all around the world were forced to work remotely – many still aren’t. Mixing personal and business use of such devices represents one of the biggest current security challenges facing SMBs, for example, due to difficulties with segregating sensitive business data from an employee’s personal email environment. Thus, BYOD policies call for creating an entire cybersecurity process of identifying and securing a personal device, without intruding on private data (like GPS location or photos) – a process that can take months or even years to build.
Although cybersecurity spending is reportedly growing, the lack of BYOD security measures is just one example that shows processes and programmes demonstrate considerable room for improvement. This includes both cybersecurity training and building a cyber-aware business culture in companies. These improvements may require even better funding and more top-level management involvement. So how can you get your CEO on board?
1) Understand the environment in which you operate
As drivers for investing in cybersecurity vary – from the shift to remote workforce and the prevalence of ransomware, to poor security practices at a company – as designated IT experts, you need to decide exactly who you are trying to persuade and influence. You might need to explain the importance of getting an internal buy-in, address the local risks for the company and explain how you plan to manage the risk. At the same time, you need to understand what is key for your company’s business operations. To do so, it may help you to engage across different teams to find out what their priorities are.
2) Explain highly technical or oversimplified information about cyber risks
Your superiors should be aware of the current security situation in the company – and they often need to be coached through this discussion. Everyone in the company must understand their personal responsibility, but it always starts from the top. Business leaders are currently following news and reading up on cyber risks, but they may lack the ability to translate that into company priorities and concrete measures. Instead, they might ask you yes-or-no questions like “Are we prepared for a ransomware attack?” Thus, it is mostly up to you to better articulate security issues and help your CEO understand the probability of the real risks for the company and what happens afterward.
3) Refrain from negative messaging
When talking about cybersecurity, IT managers often limit themselves to terrifying examples and worst-case scenarios. As Daniel Chromek, ESET CISO stated in a recent interview, these tactics often fail as people will simply feel overwhelmed and gain a defeatist mindset. And that applies not only when you are trying to raise awareness about cyber threats among your team, but also when you are talking to your boss about the necessary precautions.