In today's digital landscape, small and medium-sized businesses (SMBs) are increasingly becoming targeted by cyberattackers. While many organizations focus on preventive measures like firewalls and antivirus software, they often overlook a critical aspect — vulnerability assessment and patch management. Let's look at what it means, and why it can significantly enhance your digital security posture.
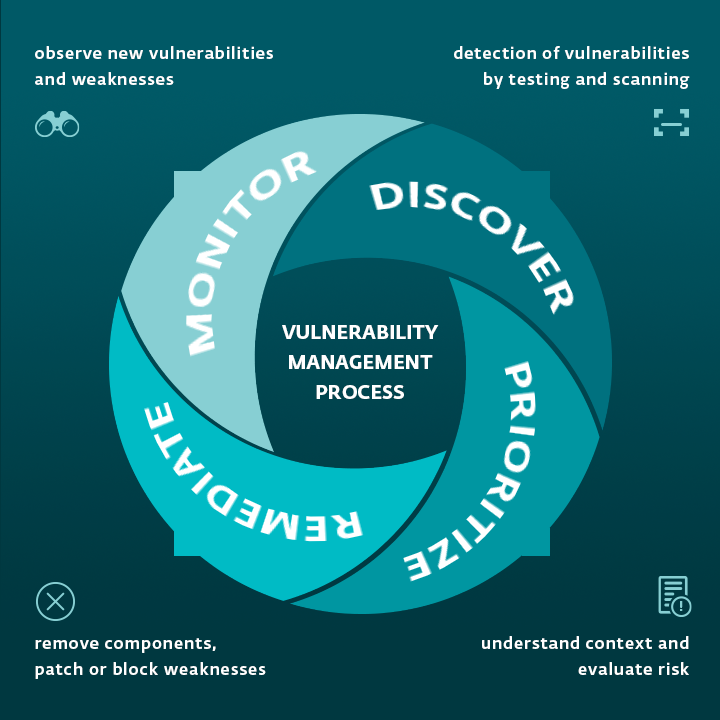
Vulnerability management means proactively identifying, assessing, and mitigating vulnerabilities in computer systems, networks, and software applications. It involves a systematic approach to detecting and fixing weaknesses before someone can exploit them. In the context of information technology, vulnerabilities refer to gaps in software that hackers can use to force the app to do something it was not developed to do. As modern organizations rely heavily on IT infrastructure to maintain productivity and process valuable data, exploited vulnerabilities can seriously impact their business continuity.
|
What is a CVE? CVE lists publicly disclosed computer security flaws, short for common vulnerabilities and exposures. Once discovered, every CVE is assigned an ID number, which can be found in the CVE list managed by the MITRE corporation.
|
Assess your digital inventory and identify weaknesses
The first step to effectively implementing vulnerability and patch management is to assess your digital inventory. That should include all software used on the company's devices and networks, as well as business email security and social engineering security tests.
Next, utilize vulnerability assessment tools to identify potential weaknesses in your systems, applications, and network infrastructure. Evaluate the severity and potential impact of identified security flaws. Prioritize them, based on their exploitability and potential consequences to your business operations.
Are platform-as-a-service solutions more vulnerable than software-as-a-service solutions? Find out in the following article.
Finally, develop a plan to address vulnerabilities, including applying security patches, updating software versions, and reconfiguring systems. Implement a regular patch management process to ensure that your systems remain secure. In some cases, there might be a need for vulnerability exceptions, usually because of business demands. If there are some vulnerability exceptions, they should be periodically reviewed and compensated for by additional controls.
Is that all? No! Your IT infrastructure is evolving, and so are the software applications themselves. That is why you should establish mechanisms for ongoing monitoring, including periodic vulnerability scans, system updates, and staying informed about emerging threats.
Does it sound too complicated? Consider employing automated vulnerability assessment and patch management tools to streamline the process and improve efficiency. Or, engage with a Managed Security Service Provider (MSSP) to identify potential weaknesses in your systems, applications, and network infrastructure.
How do you choose the right MSP? We asked Charles Weaver from MSPAlliance.
Four reasons why businesses need to address vulnerability management
1. Protecting business assets
SMBs heavily rely on their IT infrastructure, including networks, servers, and software applications, to store and process valuable business data. By identifying and patching vulnerabilities, you can reduce the risk of unauthorized access, data breaches, and potential financial losses.
2. Regulatory compliance
Many industries are subject to regulatory data security and privacy requirements, such as the General Data Protection Regulation (GDPR) and the Payment Card Industry Data Security Standard (PCI DSS). Moreover, preventive cybersecurity measures such as vulnerability management can be among the conditions required by contracts within your supply chain or by cyber insurance companies.
3. Preserving customer trust
Security incidents can have a severe impact on customer trust and brand reputation. Customers expect their data to be protected when they interact with businesses. By actively managing vulnerabilities, companies can demonstrate their dedication to maintaining the confidentiality and integrity of customer information, fostering trust and loyalty.
4. Proactive risk management
Cyber threats are continuously evolving, with new vulnerabilities being discovered regularly. Vulnerability management enables organizations to avoid potential threats by periodically scanning and assessing their systems. By addressing vulnerabilities promptly, you reduce the window of opportunity for attackers, and minimize the risk of successful cyberattacks.





