Although you thought your corporate systems were thoroughly secured, hackers accessed the customer database and stole personal and financial details. You’ve just detected a data breach. The clock is ticking. What steps do you need to take next?
The protection of EU citizens’ data falls under the jurisdiction of GDPR. If your organization handles the data of these citizens, it must comply with GDPR’s requirements. Therefore, in the event of a data leak, you must take predefined steps to protect the data of affected individuals.
In such situations, you are not just dealing with authorities and fines; your reputation is at stake too. And since attackers often publish stolen databases on the dark web, there is usually no point in playing possum.
So how do you tackle customer data breaches?
1) Inform your data protection officer and your country’s supervisory authority.
In the event of a data breach, you are obligated to inform the data protection authority (DPA), the independent public authority established by each member state of the EU to ensure and enforce the personal data and privacy laws. You must take this step as soon as you become aware of the data leak, reporting it within 72 hours. If activities of your business involve the processing of sensitive data on a large scale or regular and systematic monitoring of individuals´ personal information, accounts, transactions, etc., your security team should inform your data protection officer (DPO) first. The DPO should then notify the DPA – unless the personal data breach is unlikely to result in a risk to the rights and freedoms of affected people.
2) Fix the possible shortcomings in your network security.
There are many steps that can be taken after discovering a data breach, including:
- Change or update login credentials on company devices and implement two-factor authentication. If you still do not use 2FA, add this powerful tool for credential verification to your security measures.
- Check all network segments for traces of the breach. It’s likely that the bad actor connected on multiple segments. To keep an attack from spreading, you can reroute network traffic, filter or block traffic, or isolate all or parts of the compromised network.
- Work with an expert cybersecurity and forensics team to ascertain how the breach occurred and take the actions needed to close the breach and remove potential for any further breach.
3) Determine what kind of customer data was exposed.
To assess the scale and impact of a data breach, you need a high-quality risk management process with robust breach detection and reporting tools. If you are already experiencing a data breach, first determine what kind of data is exposed. It may take several days to determine the extent of the attack, but you need to start right away. Look for impacts to emails, phone numbers, health records, credit card data, or personal identifiers like Social Security numbers. Estimate the number of customers whose personal data are exposed. Is the data breach likely to impact the exercise of the rights of affected persons? What precautions can you take to protect customer data? You can find out in the article 6 Things You Have to Take Into Account When Handling Customer Data.
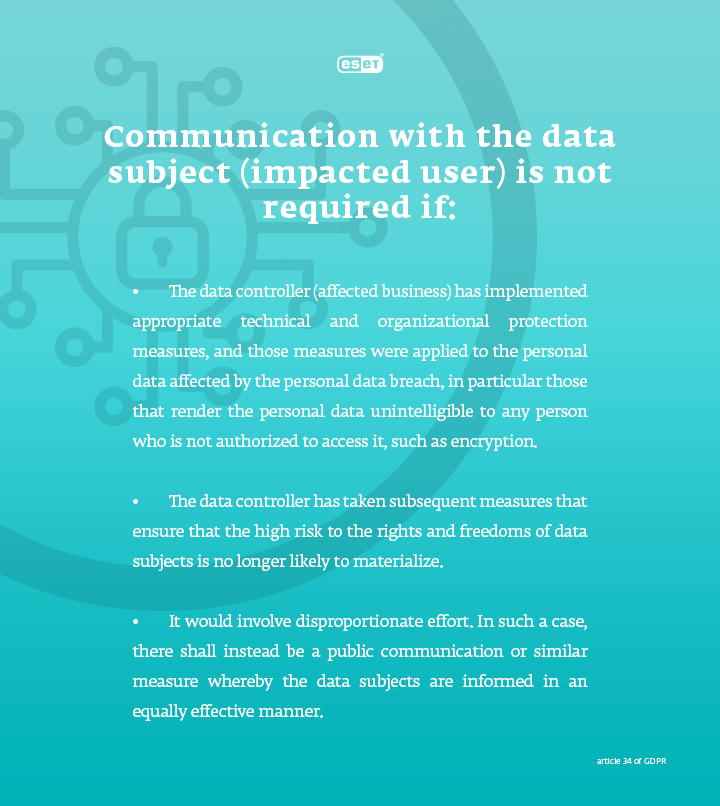
4) Contact customers whose personal data is exposed.
Organizations should thoroughly prepare for the fact that in the event of an individual data breach, they will have to contact, in some cases, hundreds of thousands of people, which can easily paralyze a company. It is necessary to inform the individuals (see exceptions in the box below) and involve a public relations or communications team in the process. Once you know what happened with the data, reach out with an apology directly to the people affected and answer the following questions: What happened? What information was involved? What is the affected business doing? What can you do if you were affected?
5) Make a review of existing security measures.
Once the personal data breach is handled, it’s strongly recommended that you explore various ways to strengthen security measures at your company. Update your cybersecurity strategy and implement better security solutions for data encryption, network monitoring, and password policies, and invest in cybersecurity training of employees.



